Digital America is publishing an excerpt of Rebecca’s essay “Al-Qaeda’s Media Strategy.” The entire essay can be found as a .pdf link at the end of the excerpt.
Abstract
Al-Qaeda was initially formed not as a terrorist organization, but as an independent Islamist military faction (Bergen & Cruickshank, 2012). The organization evolved around the ideology of the central and supreme leader Osama bin Laden (Bergen & Cruickshank, 2012). However, the ability for the group to change and adapt to different environments and cultures has allowed for the organization to spread especially to Western audiences (Bergen & Cruickshank, 2012). The evolution of their media strategy is the epitome of how al-Qaeda is adaptable (Torres, Jordán, & Horsburgh, 2006). The shift from centralized distribution of pamphlets to video and audio tapes to television and then to the Internet has allowed al-Qaeda to use the process of self-radicalization to its advantage (Lieberman & Collins, 2008). The Internet allows people to trade ideas internationally with one another without being located geographically near one another (Lieberman & Collins, 2008). The process is very much steeped in psychological processes that have the potential to be stopped at any of the three main steps (Lieberman & Collins, 2008). Three methods for halting self-radicalization including censorship of information, public education, and intelligence gathering are all examined (Neumann, 2013). The potential for backlash is great, but there is an endless array of benefits that can be achieved through a well-orchestrated public awareness campaign about the process of self-radicalization.
Summary of Media Evolution
Al-Qaeda’s move into using the Internet as their primary vehicle of propaganda has evolved the ways in which persons become potential recruits (Torres et al. 2006). Individuals viewing al-Qaeda’s material on the Internet are interacting with the information in ways that could never have imagined at the creation of the organization. Not only are people able to view and listen to the propaganda, individuals from across the world are able to connect with each other and discuss topics relating to al-Qaeda while millions miles apart from one another (Pregulman & Burke, 2012). The decentralization of the organization has allowed for more covert operations to take place, making it difficult for authorities to track these underground militants (Pregulman & Burke, 2012). However, the decentralization is counteracted with the amount of group connectedness that the Internet allows (Torres et al. 2006). With all this being said, the evolution of al-Qaeda’s media strategy has come to produce an environment in which individuals self-radicalize instead of having face-to-face contact with al-Qaeda recruiters. The discussion forums, videos, and instant messaging create an echo chamber in which persons of similar ideologies connect with one another from across the world (Lieberman & Collins, 2008). The constant exposure to this type of militant ideology is what spurs the onset of the self-radicalization process to its end of jihadization (Lieberman & Collins, 2008).
Self-Radicalization
The U.S. States Senate Committee report examined the stages of radicalization, and how the Internet media campaign waged by al-Qaeda affects a viewer during each stage (Lieberman & Collins, 2008). During the first stage known as the pre-radicalization and self-identification phase, the individual is initially interested in learning more about the ideology associated with violent Islamist extremism (Lieberman & Collins, 2008). The websites that the individual happens upon will lead them directly to the group’s enlistment pages with stories of the group’s religious beliefs and core ideologies (Lieberman & Collins, 2008). The site quickly lays the ground-work for a battle between two forces: either one is a friend or a foe, or anyone outside of the group is the foe (Lieberman & Collins, 2008). This is the seed of militarism in the site’s rhetoric. The websites are also specifically designed to target the younger populations. “With online propaganda that is often flashy, hi-tech, and interactive, the Internet has helped enable violent Islamists to deliver this message in a way that appeals to increasingly younger demographics” (Lieberman & Collins, 2008, p. 11). The next stage is the indoctrination phase in which the individuals have accepted the ideologies and core beliefs, and are now seeking ways in which to participate and further the goals of the organization (Lieberman & Collins, 2008). There are many resources that are accessible to these individuals including site design contests, books on how to participate in jihad, and prizes for competitions that include firing a rocket at a U.S. military base in Iraq (Lieberman & Collins, 2008). In the next stage jihadization, the Internet connections with the group are crucial (Lieberman & Collins, 2008). The individuals need to the Internet to connect with other recruits and organization members in order to create operation plans to carry out their own attacks (Lieberman & Collins, 2008).
Inspire, The Digital Magazine
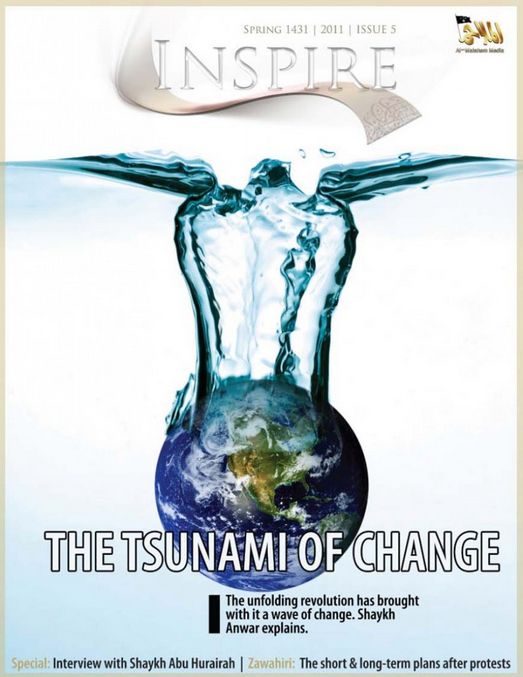
The digital magazine by al-Qaeda titled Inspire is an example of how the self-radicalization process can be completed through the use imagery and text that normalizes the content in the context of Western media. In Sivek’s article on the al-Qaeda-affiliated digital magazine Inspire, the author investigates how the design and content contributes to an individual’s self-radicalization process (Sivek, 2013). Sivek argues that because al-Qaeda has become so fragmented, that digital media outlets such as Inspire contribute to and speed up the self-radicalization process by presenting narrow interpretations of Islam and by distortions of Western culture (Sivek, 2013; Lieberman & Collins, 2008). In Fort Hood, Texas, Army Private first class Naser Jason Abdo, 22 years old, was charged with conspiracy to conduct an attack on America soil using weapons of mass destruction (Sivek, 2013). In his apartment, investigators discovered copies of the magazine Inspire including articles on how to build bombs (Sivek, 2013). Officials in Germany and Britain have also arrested and charged individuals who are suspected terrorists that were inspired by the same digital magazine to take action in the name of Islam (Sivek, 2013).
Inspire was the idea of al-Qaeda leaders in the Arabian Peninsula in an effort to sensationalize Western Muslims (Sivek, 2013). Published and edited by Samir Khan and Anwar Al Awlaki, the magazine was designed by relatively young Islamist radicalists who had extensive knowledge of digital design and media outreach strategies (Sivek, 2013). The magazine was designed to reach many different Muslim sympathizers across the world, much to the dismay of Osama bin Laden prior to his assassination in May of 2011 (Sivek, 2013). The documentation discovered by officials in bin Laden’s compound revealed the frustrations of bin Laden due to a fragmented al-Qaeda, and the effects the decentralization had on the precision and accuracy of the messaging (Sivek, 2013; Lieberman & Collins, 2008). The organization, as revealed in the documents found during the raid, was moving towards recruiting small groups of individuals motivated enough to carry out attacks on the West as lone wolves (Sivek, 2013; Lieberman & Collins, 2008). In an effort to reestablish credibility and relevancy, al-Qaeda has used the magazine Inspire to help recentralize the messaging and goals of the organization (Sivek, 2013; Lieberman & Collins, 2008).
Within the context of the self-radicalization process, Inspire uses a familiar Western-style magazine format through which to connect with potential sympathizers in the Western nations (Sivek, 2013). The format aids in normalizing the rather complicated and violent and political topics covered in the stories themselves (Sivek, 2013). The result of copying Western media styling in the Inspire magazine is almost a light-hearted, pop-culture appearance of topics relating to the militarization of religion (Sivek, 2013). For example, what may, “[look] like a how-to story for a home improvement project, laid out in steps with photos, is really a set of instructions for building a bomb “in the kitchen of your mom.” What looks like an advertisement is really a joke satirizing a “traitorous” politician” (Sivek, 2013, p. 11). What Western readers expect from Inspire based purely on the stylizing of the articles and advertisements is a medley of inspirational and aspirational stories which contributes to the acceptance of the jihadi undertones without the reader actually realizing it (Sivek, 2013). Inspire has also tapped into hip-hop culture by incorporating simple yet militant-inspired rap lyrics such as the following from Sivek’s article:
Al Qaeda is comin’ for you
So you betta shape up as our war is anew
Smashin’ and bashin’, Cashin’ and Slashin’
Is our fighting fashion
Pleasin’ the enemy is not a choice
’Cuz it betrays Islam’s voice (2013, p. 12)
Inspire not only uses innocent seeming rap lyrics to lure in youthful audiences, but the magazine also uses abbreviations familiar to young people such as “LOL” and slang words such as “diss” (Sivek, 2013). These particular elements that make the content relational to sympathizers, also contributes to the reader’s ability to accept the messaging (Sivek, 2013). If the format is normal, then acceptance of the message seems even more reasonable to the most rational of people (Sivek, 2013). Once the reader accepts the ideology, Inspire then establishes the basis of religious duty to Islam as the creation of an Islamic nation through the utilization of violence by eliciting fear and guilt of the readers (Sivek, 2013). Inspire’s Fall 2010 issue included an article entitled “O Hesitant One: It’s an Obligation!” which encouraged the action of its believers: “Until when must the love of jihad remain just another one of those hobbies of yours with which you while away your free time[?]” (Sivek, 2013, p. 14). The objective through these types of articles is to mobilize the recruits and ready them for physical violence (Sivek, 2013). Once the recruits or readers accept the ideology and mobilization narratives, then the recruit will seek out ways in which to achieve these goals (Sivek, 2013). Inspire provides step-by-step instructions for those who are planning attacks (Sivek, 2013). The magazine provides numerous ideas for waging violent jihad in the name of Islam (Sivek, 2013). For example, the magazine provided detailed instruction on how to best destroy buildings – pictures included (Sivek, 2013).
Countering Self-Radicalization
There are three types of methods that the government may use in combating and identifying the process of self-radicalization among individuals located in the U.S. Neumann argues in his article on countering Internet radicalization that there needs to be a comprehensive approach to the problem by the U.S. government (2013). This policy should establish programs that will enhance the education of the youth about these issues, counter the extreme Islamist messaging, and exploit the very systems that the groups are using to infiltrate the United States’ homeland (Neumann, 2013).
Removal or Censorship of Information
The United States is limited in removing or censoring extremist content by not only the Constitution but also by the expansive nature of the Internet (Neumann, 2013). The process of removing or blocking information would be generally unconstitutional but also impractical in the sense that there would need to be a large amount of federal oversight of website blacklists (Neumann, 2013). Also, the judicial system would have to play an integral part of this process of blacklisting and censorship in order to provide options for appeal for the affected website owners (Neumann, 2013). Not only are there constitutional limits to the U.S. ability to block or restrict certain content, the U.S. also presents itself as the “global champion of Internet freedom and the free flow of information” (Neumann, 2013, p.438). Any attempt opposite of this public image would cause international public relations nightmares. The U.S. would have to develop a dynamic system for limiting the supply of this extremist messaging in which the parameters are constantly changing every day, as is the nature of the Internet (Neumann, 2013).
Public Awareness and Education
Neumann describes the second strategy of reducing demand for extremist content as a means to increase awareness of democracy, pluralism, and peaceful ideas for advancement (2013). The author describes how the Internet can become a marketplace of peaceful ideas, but there are some challenges to creating this environment (Neumann, 2013). One of the biggest challenges to creating an open forum on the Internet for ideas is that the extremists and most enthusiastic speakers and thinkers dominate the conversations everywhere, and thus drown out the voices of moderation (Neumann, 2013). There is also a large gap in group associations and challenges in that there are millions of groups online for any kind of user, but these groups become smaller and smaller, and the users become less likely to challenge one another (Neumann, 2013). These sites essentially become echo chambers for radicalization (Neumann, 2013). There is also a disproportionate amount of young adults and adolescents using the Internet (Neumann, 2013). These young persons, while able to effectively navigate and utilize the Internet, may not be able to contextualize or analyze the arguments, and may fall victim to extremist messaging due to a lack of knowledge (Neumann, 2013).
With these challenges in mind, there are many different methods which are being used to reduce overall demand for extremist literature and messaging. The first step is for governments, communities, and parents to become aware of the processes involved in online radicalization, and the ways in which their children are being targeted (Neumann, 2013). An example of government-facilitated awareness campaigns is the U.S. National Counterterrorism Center that developed a briefing made up of slide shows and videos that can be used in town hall meetings, which encourages parents to take a more active approach in their children’s online presence (Neumann, 2013). The next step would be to facilitate the marketplace of ideas by aiding moderate voices internationally to improve their website designs and overall messaging (Neumann, 2013). For example, in 2012 the State Department hosted several online seminars for Somali bloggers based in Canada, Africa, and Europe in order for them to exchange ideas and teach each other on how to improve their websites’ functionality and appearance while also reaching out to a wider audience (Neumann, 2013). Countermessaging is also a strategy that can help to reduce demand for extremist media on the Internet. The government can play a passive role in this by bringing together groups of people affected by terrorism related incidents with media and public relations groups in order to disseminate their stories effectively (Neumann, 2013). Engagement of the extremists through their respective websites is the most direct approach the government can use to reduce demand for the radical propaganda (Neumann, 2013). In this method, the extremists are directly spoken to and, are engaged in dialogue that is counter to their ideology (Neumann, 2013). The insertion of this countermessaging is important in that these websites act as extreme echo chambers where every individual agrees on a particularly extreme message (Neumann, 2013). The government can also promote media literacy among young adults and adolescents as a long-term approach to reducing demand for terrorist-related media (Neumann, 2013). Teachers and community organizations can run classes on evaluating sources and evaluating source information for young persons (Neumann, 2013).
Strategic and Tactical Intelligence
The third strategy for countering online radicalization and terrorist recruitment involves exploiting the very means in which the terrorists’ disseminate their messages (Neumann, 2013). Law enforcement and intelligence organizations can gather strategic and tactical intelligence by simply using the terrorists’ platforms against themselves (Neumann, 2013). The goals of gathering strategic intelligence are, “to track and analyze online platforms – static websites, online forums, blogs, Twitter, videos, and discussion threads – to detect shifts in intentions and priorities, pick up on arguments, cleavages, fault lines, and new tactics” (Neumann, 2013, p. 450). For al-Qaeda, as an example, this means analysts observing the changes in battlefront interests by jihadist militants in order for the respective government organizations to track the appropriate levels of traffic for these foreign militants (Neumann, 2013). Strategic intelligence can also reveal changes in modus operandi simply by analyzing the changes in the words used in the messaging (Neumann, 2013). For example, in the extremist magazine named Inspire, Awlaki and Samir Khan, editor of the Inspire magazine, called on recruits to act as “lone wolves” (Neumann, 2013, p. 451) in attacking the United States (Neumann, 2013).
As far as tactical intelligence gathering is concerned, there are some minor things that law enforcement officials must be wary of when monitoring specific websites and social media sites for potential attacks (Neumann, 2013). Lone actors or lone wolves tend to have an extensive online history in which they participate in online forums and organizations since they may not be physically able or willing to connect with the organizations’ headquarters (Neumann, 2013). While many participants in online forums are not terrorists, there have been certain cases in which the lone actor has posted the plans for an attack online prior to the incident (Neumann, 2013). For example, Mohamed Osman Mohmoud, a 19 year old Somali-American from Portland, Oregon who had attempted to bomb the tree lighting ceremony in his hometown in 2010, had extensive connections with Samir Khan, the editor of the radical magazine Inspire, for many years (Neumann, 2013). Mohmoud was an active member of several al-Qaeda-supported online forums and had published three different articles for Khan’s online magazine, similar to Inspire, called Jihad Recollections (Neumann, 2013). These articles described how Mohmoud was going to physically and mentally prepare for carrying out an act of terrorism (Neumann, 2013).
These online sites and forums not only provide intelligence relating to potential attacks and networks of individuals connect with terrorism, but the sites also provide evidence that can be used in the court of law (Neumann, 2013). These conversations and articles, even when deleted, are forever a part of the internet. Many of the potential terrorist recruits have extensive histories of postings on Facebook and Twitter that could potentially incriminate them as far as conspiracy to commit an act of terrorism charges are concerned (Neumann, 2013). As an example of how extensive this online history can be British officials who are technological experts of the London Metropolitan Police over six months and sixteen officers to analyze the contents of one terrorism suspect’s computer and internet usage (Neumann, 2013).
Click here to read the full essay.
A GQ article, “The Most Dangerous Download on Earth” on Inspire Magazine and its role in the Boston Bombings and a number of “lone wolf” terrorist plots.
The Washington Post reported in June of 2013 that US intelligence operatives covertly sabotaged Inspire Magazine.
Here’s a CBS video and accompanying article that talks about efforts to combat al Qaeda’s radicalism and outreach strategies.
::

Rebecca Earnhardt is a junior at Virginia Commonwealth University. She’s double majoring in Political Science and Homeland Security & Emergency Preparedness. She’s planning on going into the law enforcement field when she graduate, possibly to focus on the intersection of terrorists, drugs, and criminal enterprises.